Access control systems replace physical keys with electronic credentials — keycards, mobile devices, biometric scanners or PIN pads — that are centrally managed, auditable and revocable without touching a lock. The access control system determines who can enter which spaces, at what times, and records every entry event for security review.
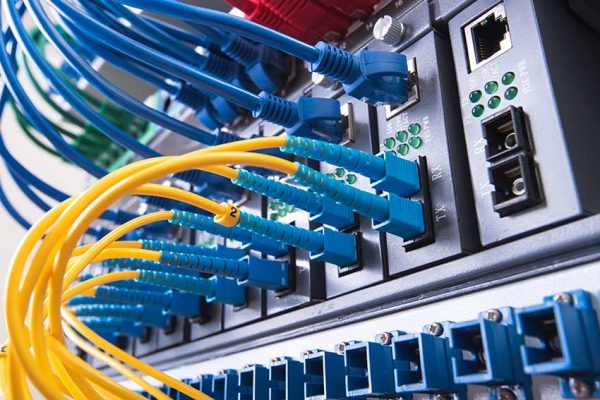
Cablify's access control scope covers the low-voltage cabling infrastructure that makes the system work: Cat6 or Cat6A cable runs to every door reader position, controller and panel enclosure connections, power cabling to electronic locks, and network connectivity from controllers back to the IDF room. This infrastructure is almost always installed alongside CCTV cabling and structured cabling — sharing pathways, IDF room space and project coordination under a single scope.
Camera mounting, controller programming, credential issuance and software configuration are typically handled by the security integrator. Cablify delivers the organized, documented cabling infrastructure that the system connects to — the physical layer that must be in place before any programming begins.